Top 12 Open Source Code Security Tools
Open source software is everywhere. From your server to your fitness band. And it’s only becoming more common as over 90% of developers acknowledge using open
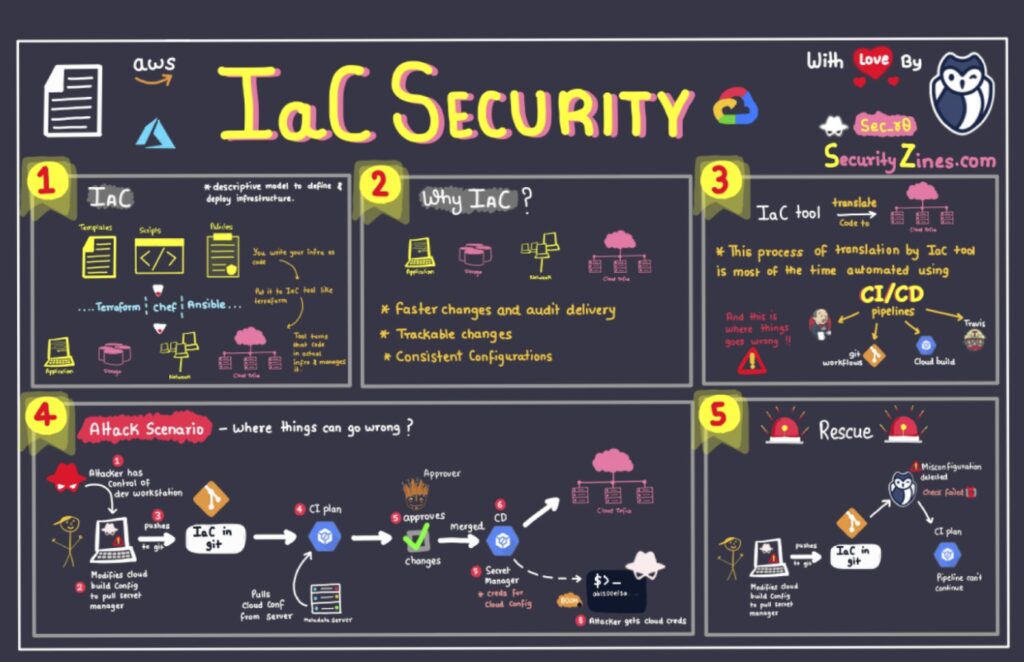
Security teams are drowning in alerts and manual tasks, and the weight of human error hangs heavy. Repetitive tasks lead to fatigue, where overlooked details can have devastating consequences. In a high-stakes environment where misconfigurations, accidentally exposed secrets, and delayed responses spell disaster, security teams desperately need tools to reduce the risk and pressure.
The rate of new attack methods and vulnerabilities emerging is increasing – 75% of teams are seeing more attacks than ever before.
However, there is a solution. A new approach to security, no-code security automation, is emerging to empower security teams to streamline their threat remediation efforts and minimize human error.
No-code security automation empowers security teams to build automated workflows without writing a single line of code. These platforms utilize a visual approach for automation, replacing potentially complex scripting with drag-and-drop functionality.
These workflows are initiated by triggers, which can be time-based (e.g., daily vulnerability scans) or event-based (e.g., an alert from a Security information and event management – SIEM). Effective threat response often depends on the ability to collect, analyze, and act upon threat intelligence in a structured manner. Understanding the core phases of threat intelligence can help streamline this process.
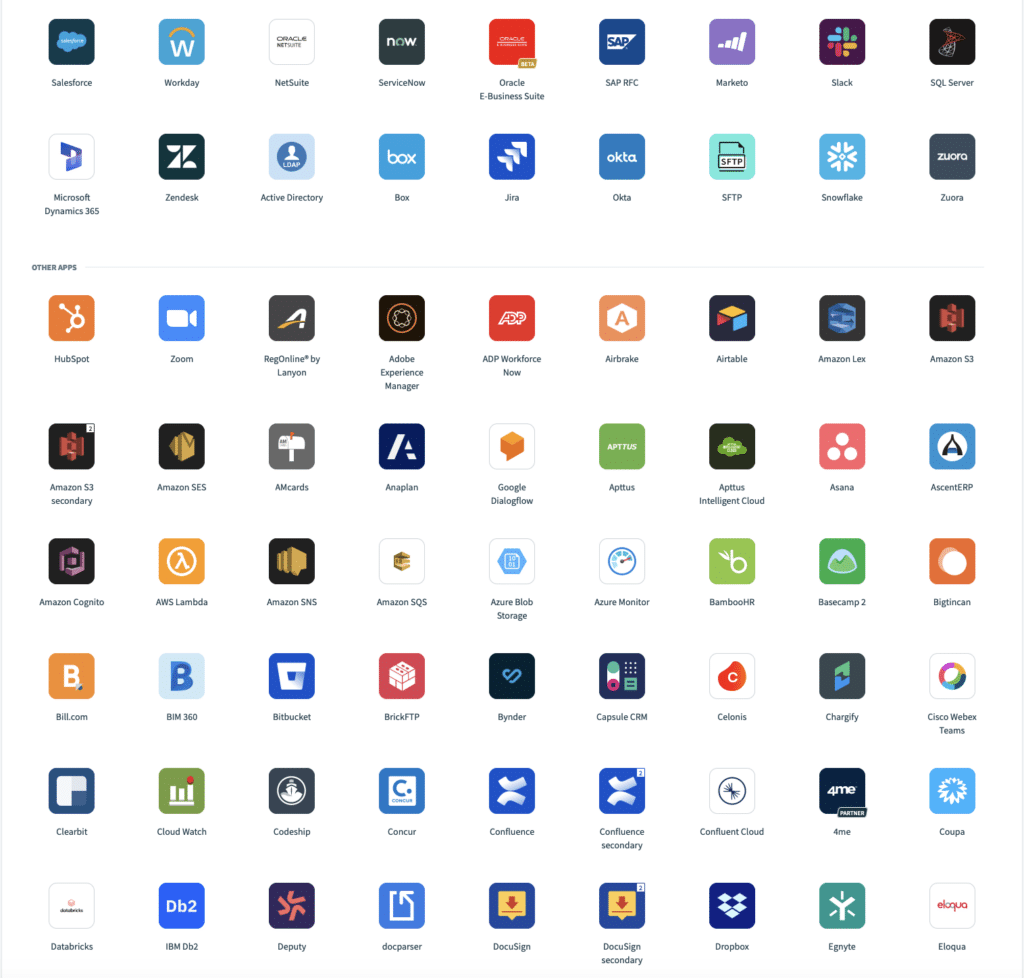
The true power of no-code security automation lies in its ability to connect with existing security and infrastructure tools. Pre-built integrations with SIEMs, vulnerability scanners, firewalls, cloud services, and other security solutions enable a unified and automated security posture.
Traditional coding provides flexibility but can also be a double-edged sword. While it grants control over every aspect of the automation, it requires significant expertise and can be time-consuming to develop and maintain. No-code security platforms cleverly abstract away the complexities, providing a human-readable way to create workflows that integrate seamlessly with various security systems. The focus on streamlining development and operational tasks aligns with the principles often championed in DevOps environments.
No-code platforms provide an accessible and intuitive way of interacting with various security systems, limiting the need to write code to connect to APIs, manage data formats, or handle error conditions.
However, just as more advanced Kubernetes use cases like custom controllers require code, the trade-off with no-code platforms is that more advanced use cases necessitate coding for added flexibility and functionality beyond the platform’s capabilities defined in human-readable formats.
Some platforms allow embedding limited code snippets within workflows. Configuration files offer a more accessible alternative for security professionals with varying technical backgrounds.
No-code security automation shines in streamlining repetitive tasks across various security domains. Let’s explore some use cases:
Picture a scenario where your SIEM detects a potential phishing or unauthorized access attempt. A no-code workflow can be triggered by this event (trigger). The workflow could then swiftly execute the following automated actions:
With the rise of containerized applications, managing vulnerabilities across environments can quickly become a challenge. While containers enable agility and scalability, they introduce new complexities in vulnerability management. As organizations increasingly rely on SaaS applications, ensuring the security of these cloud-based services becomes paramount. Adopting robust SaaS Security best practices can be incredibly helpful in mitigating these risks.
No-code platforms can integrate with various vulnerability scanners, enabling automated scanning of container images and code repositories for known vulnerabilities and misconfigurations. Specialized security solutions focused on cloud posture management have become increasingly important for maintaining visibility and control over your cloud infrastructure.
For instance, a no-code workflow could be configured to scan container images in the container registry upon each push or at regular intervals. Then, it can assign a risk score based on the severity and the criticality of the container image within your application and trigger notifications for the responsible teams based on the impacted system or application.
Similarly, no-code workflows can be designed to automate container image scanning and secret scanning within code repositories. Comprehensive security goes beyond vulnerability checks – implementing robust data monitoring practices provides crucial visibility into how sensitive data is used and potential areas of risk.
Adhering to the principle of least privilege is a fundamental tenet of access governance, ensuring that users and entities have only the minimum necessary permissions to perform their assigned tasks. However, manually monitoring and maintaining appropriate access levels across an organization’s diverse systems and applications can be daunting.
No-code security automation platforms can be crucial in enforcing least privilege principles and responding to anomalous access patterns. In the event of policy violations or anomalies, such as excessive permissions or unauthorized access attempts, the no-code workflow can automatically initiate corrective actions. Well-defined IT security policies customized to different roles and departments form the bedrock upon which effective automated security measures are built.
No-code security automation offers a powerful way to streamline security processes. However, it’s crucial to approach implementation thoughtfully to maximize its use. Here are five key considerations to keep in mind:
No-code automation shines when applied to well-defined, repetitive security tasks that follow a predictable pattern. These platforms orchestrate workflows, integrate disparate tools, and automate routine processes. However, traditional coding approaches or specialized tools may complement a no-code strategy for highly complex or nuanced scenarios requiring deep code-level analysis or intricate decision-making.
Organizations should carefully evaluate their use cases and identify the appropriate balance between no-code automation and traditional coding methods. Embedding security principles early and consistently throughout the software development lifecycle is a hallmark of mature DevSecOps practices. Assessing your current approach against established maturity models can help chart a path forward.
The effectiveness of a no-code security automation platform heavily relies on its ability to seamlessly integrate with the organization’s existing security tools and infrastructure. Robust native integrations are crucial for enabling a smooth flow of information between systems. When evaluating no-code platforms, you should prioritize those with extensive integration capabilities that align with your technology stack.
Utilizing a staging environment to test workflows and define the expected outcomes for each action within the workflow, including edge cases, can help to identify and address any potential issues that could disrupt operations or inadvertently introduce security vulnerabilities. Remember, even automated workflows can malfunction, so robust testing is crucial to ensure they operate as intended.
While no-code automation can significantly accelerate security processes, proper governance and oversight mechanisms are imperative. Organizations should establish clear policies and procedures for defining, reviewing, and approving automated workflows, particularly those involving sensitive data or critical systems.
When adopting a no-code security automation platform, it is crucial to consider the solution’s long-term scalability and flexibility. As an organization’s security needs evolve and grow in complexity, the chosen platform should be capable of adapting and supporting a more comprehensive range of automation use cases.
Assess the platform’s ability to handle increasing workloads, support more advanced integrations, and accommodate future customization requirements. Look for features that allow for extensibility and future-proofing without sacrificing the core no-code approach.
No-code security automation isn’t about replacing existing security practices but empowering them. By automating repetitive tasks like vulnerability scanning, incident triage, access control enforcement, and even secret detection within code repositories, no-code platforms free up security professionals’ valuable time for higher-level analysis and strategic initiatives.
If you’re looking for a powerful, developer-friendly, no-code solution, Spectral may be the right choice for you. We focus on secret detection and are committed to empowering developers to streamline security workflows. We can help your team avoid drowning in alerts and manual tasks.
Sign up for a free account today and experience the power of no-code security automation firsthand.

Open source software is everywhere. From your server to your fitness band. And it’s only becoming more common as over 90% of developers acknowledge using open

It’s easy to think that our code is secure. Vulnerabilities or potential exploits are often the things we think about last. Most of the time, our

Experiencing a data breach is never pleasant. Just ask any of the hundreds of businesses that suffered a data breach in the past year, exposing billions