Top 12 Open Source Code Security Tools
Open source software is everywhere. From your server to your fitness band. And it’s only becoming more common as over 90% of developers acknowledge using open
In 2018, the discovery of the Meltdown and Spectre CPU vulnerabilities sent shockwaves through the tech industry. These hardware flaws allowed attackers to steal sensitive data like passwords and encryption keys from computers, smartphones, and cloud servers. Now, in 2023, history is unfortunately repeating itself.
A new exploit called Zenbleed has emerged, taking advantage of similar speculative execution processes in AMD’s Zen architecture chips. AMD reported gross revenue of $23.6 billion in 2022, which provides a frightening insight into just how many AMD chips power consumer devices and enterprise servers worldwide.
In this blog, we’ll explain how Zenbleed works, which AMD processors are affected, and, most importantly, what you can do right now to protect yourself and your organization.
The Zenbleed exploit is a silicon-level bug that Google infosec guru Tavis Ormandy discovered. It can be exploited to steal passwords, cryptographic keys, and other sensitive data, and it affects Ryzen and Epyc Zen 2 chips, which belong to the AMD Zen2 CPU family.
Zenbleed involves abusing speculative execution, a technique modern processors use to improve performance by executing instructions before they are needed. It takes advantage of a feature in contemporary x86 processors called vector registers, which applications and operating systems use to perform math operations and process strings.
If an instruction called ‘vzeroupper‘ is speculatively executed, the processor marks the affected registers as zero and allows those registers to be used for other operations. If the processor later realizes it shouldn’t have speculatively executed the ‘vzeroupper’ instruction, it tries to undo the zeroing. However, by this point, other codes will likely use the registers. Therefore, they are no longer marked as zero, meaning their contents from the previous operation are now accessible to that other code.
Malware running on a system or a rogue logged-in user without special privileges can easily exploit this behavior. It enables the attacker to inspect data as it is processed by applications and the operating system, which can include private information like passwords.
The Zenbleed exploit significantly impacts the security of systems running AMD’s Zen 2 processors, including popular CPUs like the Ryzen 5 3600 and the entire Zen 2 product stack. The exploit allows attackers to steal data from any software on an impacted system. It’s also speculated that the Zenbleed exploit could slow down the performance of Zen 2 CPUs.
One of the major concerns about Zenbleed is its ability to execute remotely without requiring physical access to a user’s computer. Additionally, Zenbleed can operate under the radar as it doesn’t require any special system calls or privileges to exploit, which makes detecting exploitation difficult and increases the risk of unanticipated data breaches.
AMD has responded to the Zenbleed vulnerability by issuing a security advisory and releasing a microcode patch for Epyc 7002 processors. However, the tech industry doesn’t expect updates for most other impacted processors until late 2023. This delay in patches potentially leaves many systems vulnerable to the exploit for an extended period.
Here are seven actionable tips to help you stay vigilant and secure and prevent the Zenbleed exploit.
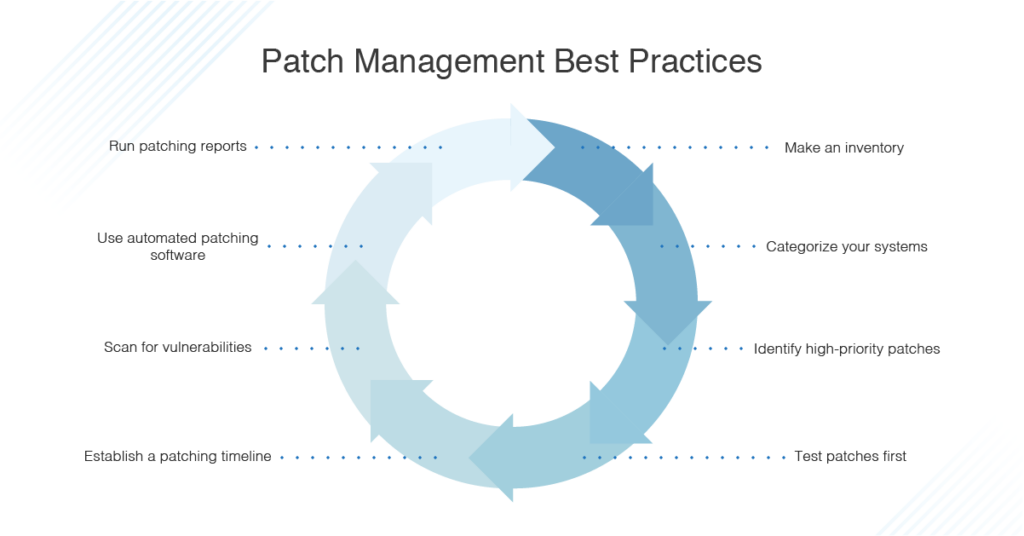
AMD has released microcode updates that address the Zenbleed issue in affected Zen 2 processors. These updates patch the vulnerability at the CPU level by adequately handling the vzeroupper instruction that was being abused. There are two main ways to get the microcode update:
Applying the microcode update is the official fix recommended by AMD and provides the complete patch for Zenbleed. Mitigations like the chicken bit may have reduced performance or don’t fully address the issue. Installing the microcode update should be a priority for any systems running vulnerable Zen 2 processors. In addition, SpectralOps can help automate and validate patching and other OS hardening best practices across your environment.
While the microcode update patches the issue at the CPU level, software vendors may also release updates to help mitigate potential exploits targeting Zenbleed:
As a best practice, regularly check your OS and software vendor sites/update mechanisms for the latest versions. Automating OS and software updates is highly recommended for the newest mitigations. Combining microcode fixes with software updates provides overlapping layers of protection against potential exploits of the Zenbleed bug.
On Linux and FreeBSD systems, you can set the ‘chicken bit’ CPU flag to prevent abuse of the vulnerability. The ‘chicken bit’ is a hardware mitigation on AMD Zen 2 processors that prevents the speculative execution behavior leading to the Zenbleed vulnerability.
Linux:
modprobe msr
# wrmsr -a 0xc0011029 $(($(rdmsr -c 0xc0011029) | (1<<9)))This will persist across reboots.
FreeBSD:
cpucontrol -m DE_CFG:9=1
To make this persist, add the following to /boot/loader.conf:
cpu_microcode_load="YES" cpu_microcode_name="/boot/zen2_microcode.bin"The chicken bit disables specific speculative execution capabilities of Zen 2 CPUs that Zenbleed abuses. However, it can result in reduced performance in some workloads.
The chicken bit mitigation can be useful if microcode updates are not available for your system yet, but updating the CPU microcode is recommended over the chicken bit where possible.
Simultaneous multithreading (SMT) allows a single physical CPU core to act as two logical cores by running two thread contexts in parallel. However, SMT can allow cross-thread data leakage through side-channel attacks like Zenbleed, as the two threads share certain internal processor states like caches.
Disabling SMT prevents this cross-thread leakage by only allowing one thread context per physical core. It can be disabled in the BIOS/UEFI settings of most systems. On Linux, you can also disable it temporarily by using the kernel parameter nosmt
The drawback of disabling SMT is reduced performance, as you lose the extra throughput of having two threads per core.
Modern CPUs from AMD and Intel provide virtualization capabilities like AMD-V and Intel VT-x to support running virtual machines (VMs) and containers.
These virtualization features can be used to provide additional security isolation between the host system and virtualized environments, making it much harder for speculative execution attacks like Zenbleed to leak data from inside VMs. Some specific capabilities that help mitigate Zenbleed in VMs are:
The advantage of this approach over disabling SMT is that you can isolate the sensitive VMs/containers without compromising overall system performance. Also, SpectralOps validates hypervisor configurations and ensures proper policy enforcement for isolation, as per security hardening best practices.
Although the Zenbleed attack mainly abuses speculative execution triggered by the vzeroupper instruction, other instructions can also lead to speculative executions. These include instructions like:
Random number generation functions, searching/sorting algorithms, neural network inference, and image processing are some key areas you need to consider since they tend to use AVX and SSE.
Organizations should consider running highly sensitive workloads on non-vulnerable hardware, away from systems affected by Zenbleed. For example:
Non-vulnerable hardware could include older AMD processors or Intel-based systems unaffected by this specific issue. Using instance types/families that don’t use Zen 2 CPUs could be an option for cloud environments.
The recent discovery of the Zenbleed vulnerability in AMD’s Zen2 processors serves as an important reminder that a security monitoring strategy requires constant vigilance. While AMD has released mitigations, the potential for new exploits means organizations must remain proactive.
Implementing a layered security strategy with controls like patching, encryption, access management, continuous security monitoring tools, and more can significantly reduce your attack surface and risk exposure. Though no single solution is foolproof, taking a defense-in-depth approach makes it much harder for attackers to be successful.
With Spectral, you can automate the process of assessing configurations and protecting access credentials, keys, and other sensitive data. Spectral provides the visibility, detection, and response capabilities security teams need.
Get a free trial today.

Open source software is everywhere. From your server to your fitness band. And it’s only becoming more common as over 90% of developers acknowledge using open

It’s easy to think that our code is secure. Vulnerabilities or potential exploits are often the things we think about last. Most of the time, our

Experiencing a data breach is never pleasant. Just ask any of the hundreds of businesses that suffered a data breach in the past year, exposing billions