Top 12 Open Source Code Security Tools
Open source software is everywhere. From your server to your fitness band. And it’s only becoming more common as over 90% of developers acknowledge using open
Once written off as a failed CMS incapable of generating a significant user base, Microsoft’s SharePoint has continually defied expectations to become one of the most widely-used ECM and Collaboration products ever. It caters to over 200 million users and 250,000 organizations, including 85% of Fortune 500 companies.
SharePoint is a user-friendly intranet portal and provides a consolidated center for document sharing, tracking, and overall project management. But with all the value it brings to businesses, SharePoint has become a platform too complex to completely secure without impacting collaboration flexibility.
SharePoint may appear simple at first, but there is more than meets the eye under the hood. Some of the major SharePoint paradigms include:
You can find more details about SharePoint permissions here.
Despite all the security options, permissions, and access controls that come with SharePoint, the collaboration tool is still riddled with unpatched security holes. Below, we cover 8 of the most common risks and vulnerabilities associated with SharePoint and what you can do to secure your organization from them.
SharePoint Site Owners must make the critical decision of whether or not they should share the site with external users. With the potential benefits of increased productivity and collaboration come the security risks associated with sharing. Without proper access protocols, even a visitor to the site can add another user and make them a member.
To minimize the downside, Site Owners can disable sharing privileges from Settings > Site permissions > Advanced permissions settings > Access Request Settings.
The ability to share a site is a subjective matter. As a Site Owner, you may want to control security by disabling sharing for department or private team sites but leave sharing enabled for project sites to promote collaboration.
Not clearing SharePoint properties from a document before sharing it can have grave consequences. It can lead to information leakage, compliance violations, and confusion, showing a lack of professionalism.
SharePoint properties often contain metadata such as the author’s name, the date the document was created, and the date it was last modified. This information can be sensitive and should be removed before the document is shared with others. Additionally, SharePoint properties may contain information specific to an organization’s internal processes and workflows, which may not be relevant or appropriate to share with external parties.
To clear SharePoint properties from a document, select the document in question, go to “File” > “Info” > “Properties” > “Remove Properties” or “Remove All Properties and Personal Information”.
When you sync document libraries from SharePoint to your local computer, there’s a chance that some files or folders may get accidentally deleted, and those deletions will then be synced back to the SharePoint library, effectively erasing the files from the server as well.
Here are a few SharePoint features you can try to prevent data loss:
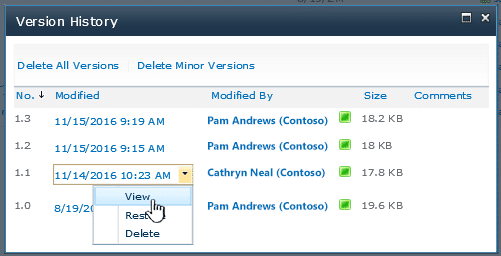
Alternatively, you can go to the library or site settings and set the “Offline client availability” option to “No” or revoke permissions for specific users to the library or site they are syncing.
Without the required Data Loss Prevention (DLP) policies, files across your SharePoint are prone to get duplicated, mislabeled, or even deleted. And if you don’t have proper data lineage tracking, it can be hard to figure out where the data came from, if data loss has even occurred and whether any unauthorized users were involved.
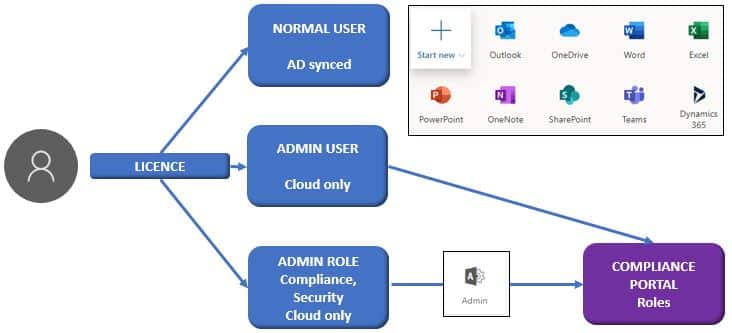
DLP policies are rules and settings that can help you prevent sensitive information from leaving your organization and can be created and managed through the Microsoft Purview compliance portal.
Having too many Group Owners on SharePoint can be a security problem because it becomes challenging to manage access controls and protect sensitive information. Keeping track of who has access to what becomes laborsome, which increases the risk of accidental data breaches. Remember that getting Group Owner privileges means you can delete a site.
It’s important to limit the number of group owners and have proper policies and procedures to ensure that access to sensitive information is controlled and limited to necessary authorized users only.
No one wants their files getting accessed by unauthorized individuals, whether it be through accidental discovery or intentional snooping by colleagues.
You have a few options to prevent unauthorized access to your files:
Similarly, you can define specific permissions on a file or simply store sensitive information in your own OneDrive account if the above options are a tad complex.
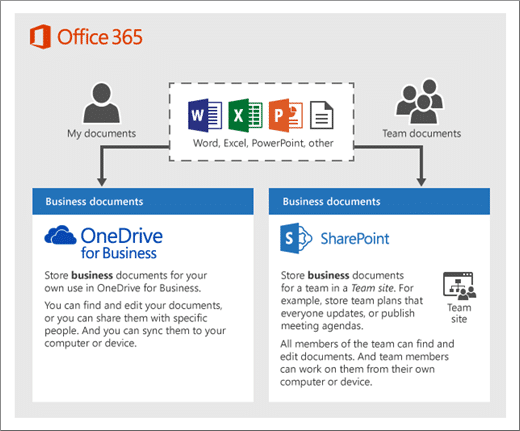
Deciding who should manage a SharePoint site is another major responsibility. SharePoint offers two common security models for intranets: role-based and site-based. The role-based model is based on users’ roles within the organization and is controlled by a small group of users. The site-based model relies solely on the site objective and is controlled by the Site Owner. While the former allows for standardizing security groups and naming conventions (although tedious to maintain), the latter model improves user adoption but may lead to too many redundant groups.
There’s no one-size-fits-all solution. Depending on your company’s culture, one way to tackle this is to have a blended approach. For example, the IT team can manage security for departments or sensitive sites but have business or site owners take control over team sites.
Ignoring software updates on SharePoint is like wearing a “Kick Me” sign. You’re not only missing out on all the hot new security patches which will leave you vulnerable to all sorts of cyber risks but also indirectly disrupting your workflows with data loss that arises from compatibility issues.
In late 2019, hackers infiltrated the U.N.’s servers by exploiting a vulnerability in SharePoint. They compromised 40+ computers. Microsoft had already issued a fix to this vulnerability early that same year, but unfortunately, the U.N. had failed to update its servers with that fix.
The only way around this for you is to be prompt when installing SharePoint software updates that address known security issues. To that end, you can either use the Microsoft Update service or get these updates from the SharePoint Central Administration website.
SharePoint is a powerful tool, but it’s not immune to vulnerabilities or unauthorized access when you’re not careful. By taking a proactive stance on security, you can protect your business from potential threats. The importance of regularly reviewing to update security settings, training users, and monitoring for suspicious activity cannot be overstated.
Similarly, businesses can no longer afford to overlook the importance of securing code when engineers build features for SharePoint sites. Spectral helps with application security by identifying potential vulnerabilities in code throughout the development lifecycle with real-time threat detection to help you stay compliant with regulatory requirements. It also gives you total control over who can access and modify your SharePoint data, so you can rest easy knowing your sensitive information is safe. Learn more about Spectral here.

Open source software is everywhere. From your server to your fitness band. And it’s only becoming more common as over 90% of developers acknowledge using open

It’s easy to think that our code is secure. Vulnerabilities or potential exploits are often the things we think about last. Most of the time, our

Experiencing a data breach is never pleasant. Just ask any of the hundreds of businesses that suffered a data breach in the past year, exposing billions