Top 12 Open Source Code Security Tools
Open source software is everywhere. From your server to your fitness band. And it’s only becoming more common as over 90% of developers acknowledge using open
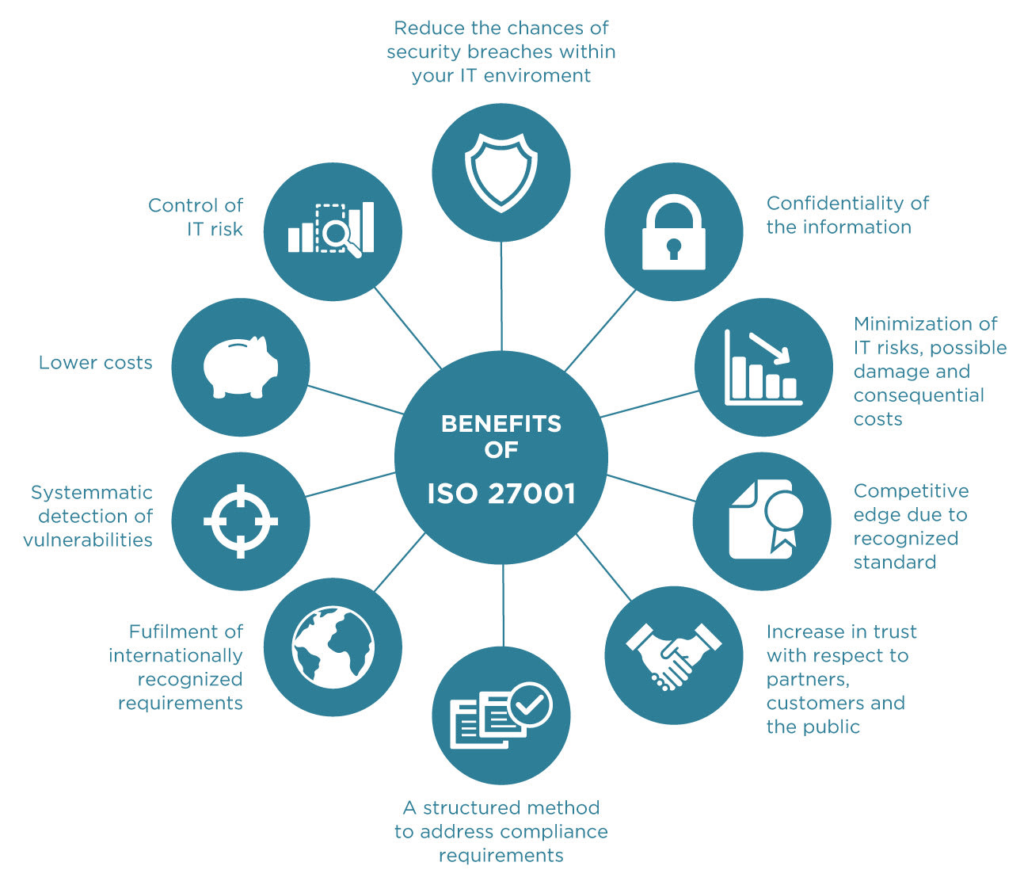
For organizations looking to reassure customers that excellent data governance is one of their guiding principles, and that they’re doing everything in their power to mitigate the risk posed by cybercrime, ISO/IEC27001 certification is one of the best ways to demonstrate that commitment. Nevertheless, it’s a high standard to achieve. According to data supplied by ISO.org, only 28,426 companies worldwide had achieved the certification by 2022. How can you give yourself the best chance of emerging from the audit process with flying colors?
Of course, in order to pass the certification, you’re going to need to pass through an external audit. But to give yourself every chance of emerging with flying colors, it’s smart to use your internal resources to help run through a test preparation checklist. In that spirit, we’d like to present The Ultimate ISO 27001 Requirements Checklist which we’ve prepared based on our extensive experience helping organizations worldwide track and secure their data stores.
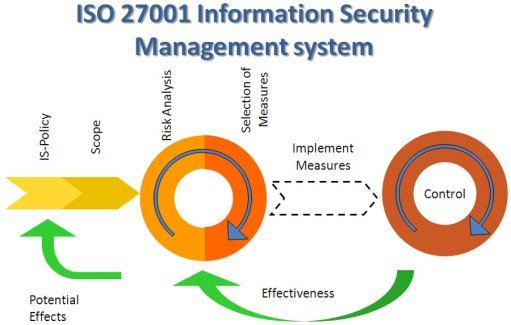
ISO/IEC27001 is a world-leading information security standard. It includes a set of detailed requirements for demonstrating that your organization is implementing a professional and reliable Information Security Management System (ISMS). It was introduced in October 2005 as a replacement to the BS7799-2 standard.
Specifically the standard covers:
The core requirements to be certified as compliant with ISO 27001 are:
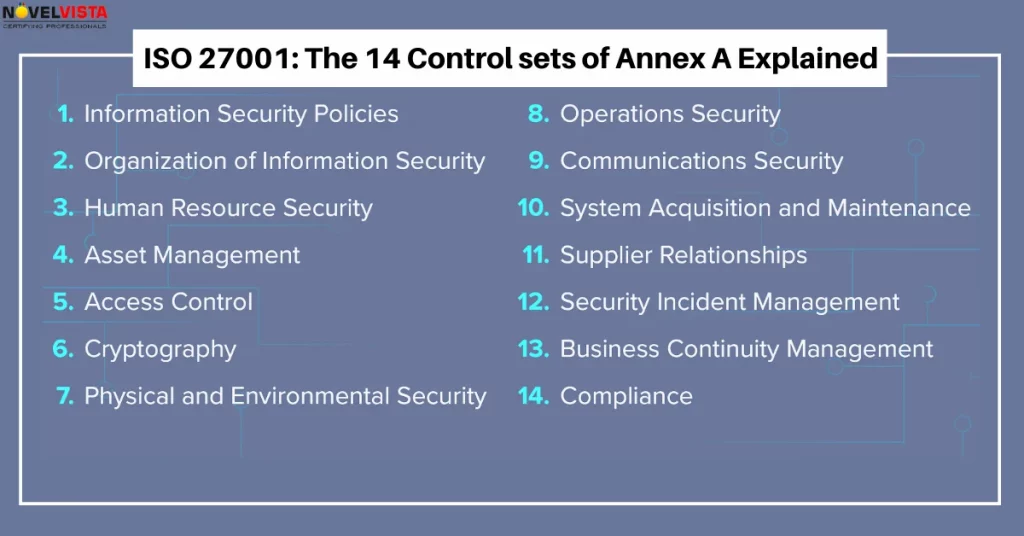
Cumulatively, these are listed, in full, as Annex A to ISO 27001 which provides the full list of controls that are necessary to demonstrate in order to pass the audit. Those looking to obtain a more detailed list of requirements necessary for successful passage of the certification standard should consult this source.
An Information Security Management System is at the core of the ISO 27001 certification process. In fact, the Standard sets down policies and procedures that involve technology, people, and processes related to its safe upkeep.
The certification will evaluate what
Additional areas that organizations will need to demonstrate competence and proper governance in order to emerge with the certification include:
For organizations embracing modern development methodologies — such as DevOps and DevSecOps — passing through this certification can provide an enormous safeguard. With robust governance of ISMSs assured, rapid development processes can proceed unimpeded by the risk of the failure of any systems which are crucial to the development process.
In order to pass the ISO 27001 standard, organizations need to go through an auditing process. Nevertheless, a self-assessment is a great way to probe your level of preparedness for that process without the associated cost and stress.
A checklist provides a systematic framework for going through the self assessment process. It should provide a logical and robust means of assessing your internal readiness to take the actual audit.
Because every organization is unique, we recommend taking the time to develop an internal and proprietary checklist that can integrate the specific information as it relates to your business. However, the model we have provided below should provide a good starting point.
As your own individual journey towards the audit evolves, it may also be worth periodically updating this in order to reflect those areas that you feel may require more or less attention.
Our recommendation is to start with an expertly-prepared requirements checklist for passing the audit.
You can add items to the checklist if you’re particularly worried about your ability to demonstrate know-how in a particular area of the audit.
Alternatively if you’re really sure that you’ve already excelled in a certain domain of competence – like support awareness – then you can skip over that in one of your internal requirements checklists.
Together this will give you the best chance of passing through the audit with flying colors.

Open source software is everywhere. From your server to your fitness band. And it’s only becoming more common as over 90% of developers acknowledge using open

It’s easy to think that our code is secure. Vulnerabilities or potential exploits are often the things we think about last. Most of the time, our

Experiencing a data breach is never pleasant. Just ask any of the hundreds of businesses that suffered a data breach in the past year, exposing billions