Top 12 Open Source Code Security Tools
Open source software is everywhere. From your server to your fitness band. And it’s only becoming more common as over 90% of developers acknowledge using open
Source code leaks happen. When they do, you need to act fast to secure your assets and your development environment. The longer an insider threat incident lingers, the costlier it gets for organizations.
A recent report indicated that the average incident takes 77 days to contain. Incidents that take more than 90 days to contain cost organizations an average of US$13.71 million annually, where incidents that are mitigated in less than 30 days cost roughly half as much.
To respond quickly, you need a thorough plan of action. Follow these six steps to alleviate a source code leak, associated costs, and negative public reaction. And learn how to secure your source code to protect against future leaks.
Identifying the source of the code leak can range from easy to more obscure. Consider these examples:
To identify the leak, you might require extensive and expensive data forensics to detect the source. For this investigation, determine the type of leak:
By gaining this perspective, you’ll have a better understanding of how to contain the leak.
Depending on the source and type of leak, take the necessary actions to contain it.
Because source code leaks commonly contain login credentials, application programming interface (API) keys, access tokens, and other confidential information, prevent further leakage:
To avoid recurring leaks, consider any piece of information that might risk further damage.
A source code leak, even when you try to contain it, can disrupt service to your customers. The leak itself might include personal information that can potentially expose your clients to future security risks. Therefore, you need to both inform your customers about the incident and control the message itself so they don’t hear the news from external sources, such as the media.
To mitigate potential damage to your organizational reputation, maintain transparency and professionalism with your customers during the process. Provide a public account of the action your company has taken to plug the leak and reduce the damages. In extreme cases, when a leak involves exploitable, publicly identifiable information, include a remediation process such as credit monitoring and identity theft protection.
Most source code leaks from external sources are due to a lack of security practices, complacency, and neglect. Look at your entry and end points and make sure they are secured.
Two of the most common attack vectors are cross-site scripting and Structured Query Language (SQL) injections. Both rely on faulty input-field verification that can lead to unauthorized access.
When you expose user input fields, such as in login or sign-up forms, validate them before you pass the input to a database or plugin where it might be used to leak data.
Security researchers and hackers are always on the lookout for software bugs that might be used in an exploit. The problem of “old software” is exacerbated by the fact that, when an exploit is resolved, hackers can reverse engineer the fix to create an exploit that still functions on unpatched, outdated software. Therefore, check your server software for the latest updates and install them.
Updating the server software to the latest version is not sufficient. Plugins and third-party components are themselves a target of exploitation. Map the plugins and third-party components that your organization uses and update them with the latest security patches.
Endpoint security is available through the antivirus software used to protect employee desktops, laptops, and mobile devices. But, endpoint security has evolved so that it now quickly detects, analyzes, blocks, and contains attacks in progress.
Today, many people work from home and more companies have bring-your-own-device (BOYD) options for employees. Regardless of where your employees are located, implement an endpoint security policy on every device that’s used to run your business.
To secure assets with a multi-layered security operation, you need to know where your critical assets are located, whether for HR, Legal, Marketing, or IT. To prevent a single point of failure from toppling your entire organization, implement the tools and security practices you need to prevent, detect, and respond to any threat in real time.
For example, you might use a tool that scans incoming communication for phishing activities as a first layer of defense against infiltration through human engineering. Or consider a tool that integrates into the continuous delivery or continuous deployment (CD/CI) pipeline to block an accidental code-commit from posting proprietary source code and secrets to a public code repository.
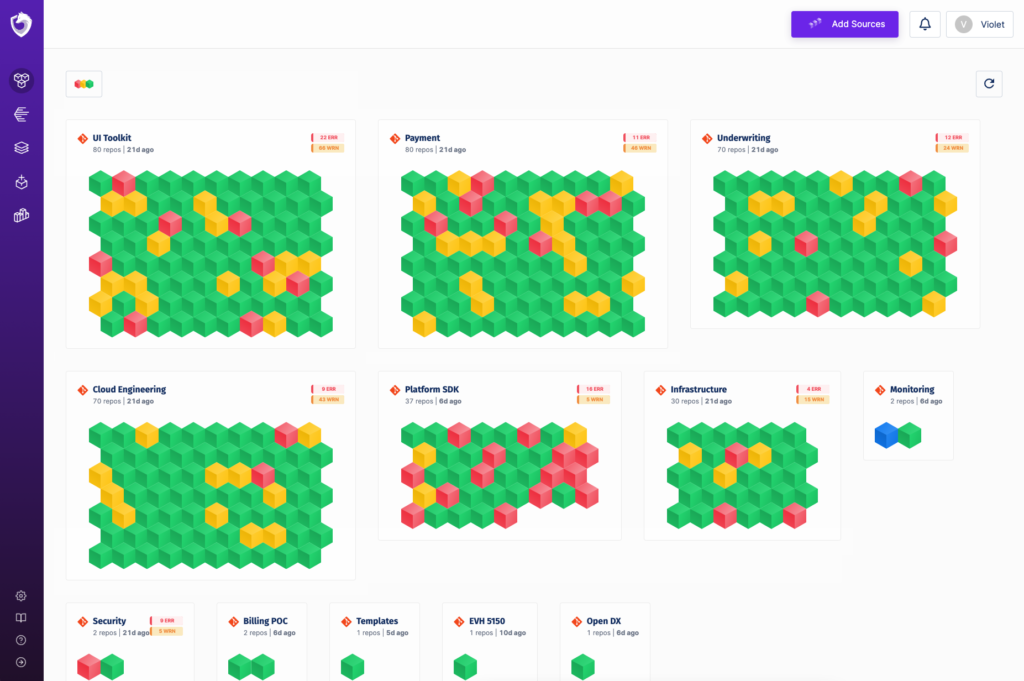
Securely safeguard your source code to negate or mitigate source code leaks. To secure your development environment and avoid future code leaks, take advantage of the continuous scanning and powerful security coverage of the Spectral Ops platform. This continuous monitoring system offers:
Regardless of your technology stacks and programming languages, the Spectral Ops platform integrates easily to provide complete security coverage without disrupting developer workflow.
By continuously monitoring your CD/CI pipeline, the Spectral Ops platform automatically detects and blocks (with notification) accidental source code leaks because of human error.
Even a professional DevSecOps expert can miss a server configuration issue. The Spectral Ops platform automatically analyzes your Git server configuration, so you can rest assured that your server conforms to industry best security practices.
The platform also sanitizes another blind spot—your Git history. Even well after a developer removes your secrets from your code, they might still reside in your Git history. By automatically sanitizing your Git history, the Spectral platform ensures no lingering secrets remain.
Developers might take shortcuts by embedding such secrets as database passwords, API keys, and access tokens right in the source code to make it easier for them to access them later. Unfortunately, this practice has no regard for security practices. To minimize the risk of auxiliary damage even in cases where source code leaks, automatically scan your code by using machine learning techniques and eliminate exposed secrets.
Use a tool that matches the unique characteristics of your organization. Create custom detectors to identify secrets in the code that use structures unique to your organization that a regular scan might otherwise miss.
Some security solutions send your code for analysis in the cloud. Instead, use only local scanning to make sure your organization’s source code remains on site, free from the risk of a third-party vulnerability exposing your code.
By using a continuous monitoring system, even if a source code leak happens, you can provide auditors with the required tools to trace and remediate the incident in the fastest possible time.
By following these steps and integrating a complete security solution, you can recover quickly from a source code leak. But don’t wait for a source code leak to happen. See how Spectral Ops can protect you from source code leaks and secure your DevOps pipeline today. Request a demo.

Open source software is everywhere. From your server to your fitness band. And it’s only becoming more common as over 90% of developers acknowledge using open

It’s easy to think that our code is secure. Vulnerabilities or potential exploits are often the things we think about last. Most of the time, our

Experiencing a data breach is never pleasant. Just ask any of the hundreds of businesses that suffered a data breach in the past year, exposing billions