Top 12 Open Source Code Security Tools
Open source software is everywhere. From your server to your fitness band. And it’s only becoming more common as over 90% of developers acknowledge using open
A high-profile case hangs in the balance. Suddenly, court systems are paralyzed. Evidence is locked away, replaced by a ransom demand.
Every law enforcement agency’s nightmare is alarmingly common – 96% of organizations were hit by ransomware in the past year, according to Cisco’s 2023 report.
Exposed API keys, forgotten cloud configurations, outdated systems – these seemingly small vulnerabilities are the entry points relentless cybercriminals exploit. Traditional security tools often miss these hidden threats in the justice system, where data integrity is everything.
But there’s a solution, which comes as a CJIS security policy.
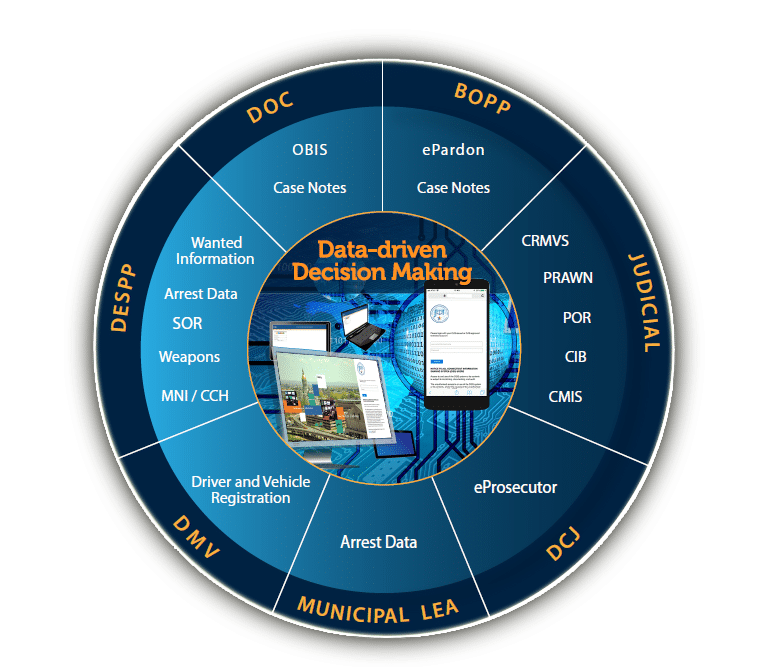
The FBI developed the Criminal Justice Information Services (CJIS) Security Policy. This policy sets strict guidelines to protect Criminal Justice Information (CJI). It focuses on safeguarding confidentiality, integrity, and availability. CJI encompasses sensitive data like fingerprints, criminal histories, and ongoing case details. Law enforcement agencies across the United States handle it.
The CJIS Security Policy enforces strict access controls for sensitive data, protecting against accidents and attacks. However, ensuring compliance in a complex landscape where supply chain vulnerabilities pose additional risks. Proactive security solutions that scan your entire codebase, configuration files, and public-facing assets help you discover hidden vulnerabilities and potential data leaks, making compliance much more achievable.
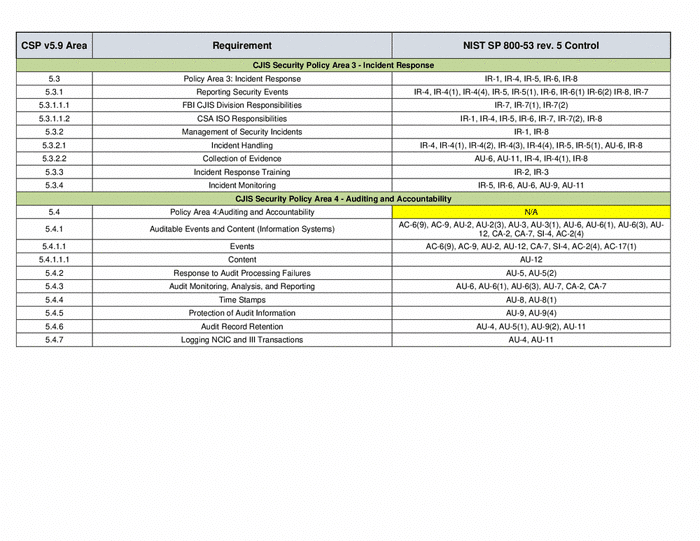
Critical aspects of the CJIS Security Policy include:
Follow these 7 CJIS-mandated steps for a more resilient organization.
Success with the CJIS Security Policy starts by knowing your organization’s CJI risks. Do something other than a generic risk assessment. Go beyond traditional risk assessments with specialized tools that scan your code, infrastructure, and public-facing assets for exposed secrets (API keys, database credentials, etc.), misconfigurations, and proprietary code leaks. These vulnerabilities often slip through the cracks of standard security checks but are prime targets for exploitation. Choosing the right secret scanning solution is vital in automating the discovery of these risks.
A targeted approach is not merely advised but mandated by the FBI for agencies to achieve accurate CJIS compliance.
Here’s what to do:
Before implementing security measures, understanding your CJI landscape is crucial. Begin by meticulously mapping where Criminal Justice Information (CJI) exists within your organization. Remember physical records when thinking about security. Paper files, storage locations, and offline devices with CJI are all important. Tracking where all your data is stored is essential for full CJIS compliance.
Once you’ve mapped your CJI footprint, thoroughly analyze potential risk points. Are outdated systems leaving you vulnerable? Do you have strong practices around employee access changes to prevent lingering permissions?
A good risk assessment considers both deliberate attacks and the risk of accidental leaks. To ensure no weaknesses slip through the cracks, avoid generic checklists. Use CJIS-specific tools and checklists to strengthen your security assessment. These help you identify problems and take immediate steps to protect CJI.
Accidental or malicious unauthorized access poses a considerable risk to CJI. The CJIS Security Policy provides the framework to stop it. Your focus should be on robust access control to block unauthorized entry.
Implement these best practices to protect your invaluable data:
By only giving staff the absolute minimum access they need to work, the least privilege principle drastically reduces attack surfaces and prevents accidental data misuse – this is fundamental for robust access control. Modern solutions also focus on verifying source authenticity to enhance access control and protect the integrity of your systems.
Regular changes, complexity rules, and secure password management tools are mandatory with CJI. Weak credentials are one of the most easily exploited entry points.
Regular access reviews are essential for security. Check for these risks:
A one-time audit isn’t enough – your security must evolve alongside your operations.
Modern access control solutions enable automation, real-time monitoring, and granular permissions management. Prevent oversights and security issues in your CJI access management. Where possible, use tools to simplify the process.
Strict access controls are a crucial part of the CJIS Security Policy. Augment your security measures with continuous monitoring tools that alert you to exposed credentials or misconfigurations that could allow unauthorized access, letting you act before a breach occurs. Most importantly, they keep the sensitive data you manage safe.
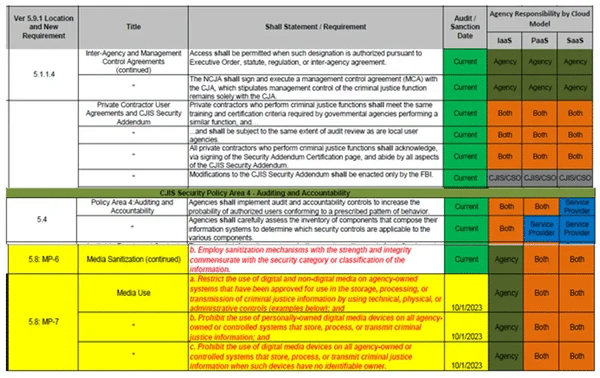
To ensure safe data handling, the CJIS Security Policy provides specific rules that adapt to your organization’s workflows. Start by focusing on the areas your assessment flagged as potential weak points:
Target security upgrades based on your risk assessment for optimal resource allocation.
The CJIS Security Policy isn’t a static document for tech staff alone. Actual compliance demands embedding security practices into organizational culture. Good training and identity security are vital to keeping CJI safe. Ensure your staff knows how to handle CJI in every situation.
Critical Topics for Effective CJIS Training:
More than occasional workshops are needed for CJIS compliance, too. Comprehensive onboarding training sets the foundation for secure practices. Regular updates on policy changes and systems keep your staff sharp. Consistent training cultivates a culture where security is part of everyone’s work. Consider innovative approaches like gamification to make security training engaging and effective.
Handling CJI makes you a target. Never assume you’re too small or unimportant to be attacked. An effective incident response plan minimizes damage and demonstrates proactivity for future audits. It goes beyond tech fixes to establish transparent processes for everyone involved.
What to do for a fast response:
In a crisis, a clear plan enables a swift response. Equip your team with precise steps, not improvisation, to limit damage and facilitate recovery and assessment.
Establish a Communication Chain:
Predefined communication channels minimize confusion during a breach, reducing impact and enabling a swift, coordinated response.
A robust incident response plan must go beyond technical steps. Staying informed about evolving cyber threats helps you anticipate attack vectors, strengthen your defenses, and develop more effective response strategies.
Meeting initial requirements is just the start. Doing so ensures your practices remain strong and your ability to demonstrate compliance keeps pace.
Detailed records aren’t just red tape; they’re evidence and analysis tools. Detailed logs, incident reports, and staff assessments are powerful tools. They help you improve security and prove your commitment to CJIS compliance.
Key Record-Keeping Focus Areas:
Don’t let audits be stressful – use them as opportunities. Examine each finding to address its root cause, not just the immediate fix.
Internal assessments are pivotal in ongoing CJIS compliance, but sometimes, fresh eyes make all the difference. Independent audits offer a fresh perspective on your security program.
CJIS compliance isn’t just about following a checklist but building a resilient organization that safeguards the data driving justice. Proactive security, focusing on identifying exposed secrets, misconfigurations, and potential leaks, is essential. Investing in the right tools and ongoing vigilance empowers you to collaborate effectively with other agencies, fosters a security-conscious team, and protects the integrity of your work.
Ready to strengthen your CJIS security posture? SpectralOps automates the discovery of hidden vulnerabilities, giving you actionable insights to achieve proactive compliance. Start today.

Open source software is everywhere. From your server to your fitness band. And it’s only becoming more common as over 90% of developers acknowledge using open

It’s easy to think that our code is secure. Vulnerabilities or potential exploits are often the things we think about last. Most of the time, our

Experiencing a data breach is never pleasant. Just ask any of the hundreds of businesses that suffered a data breach in the past year, exposing billions